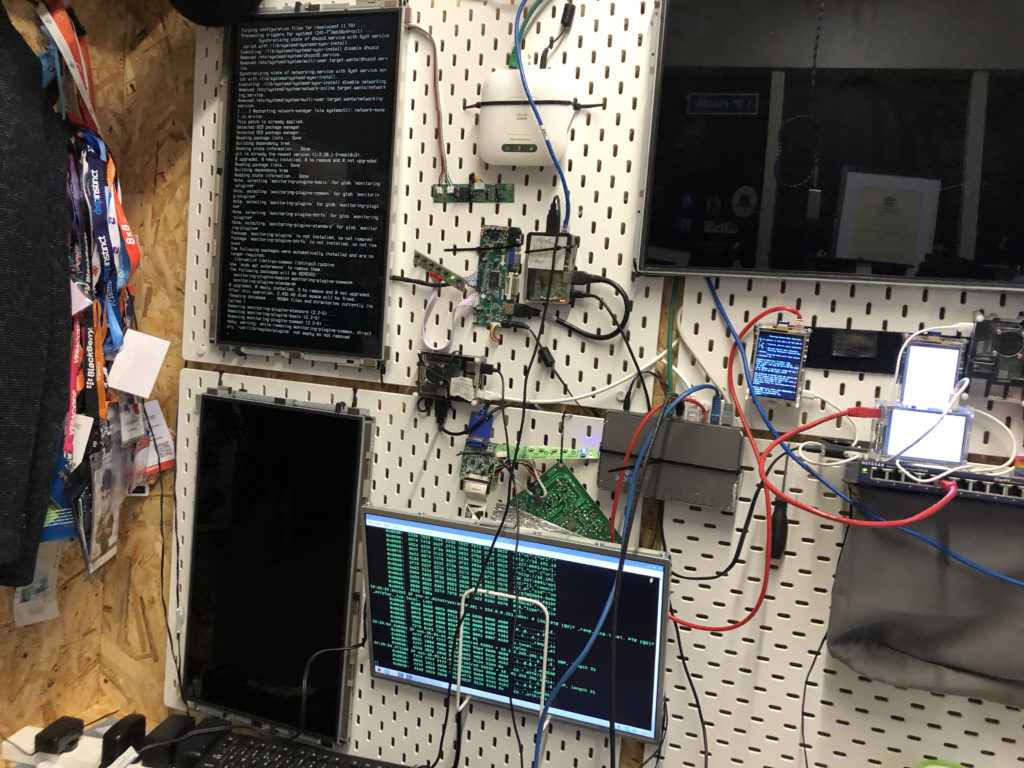
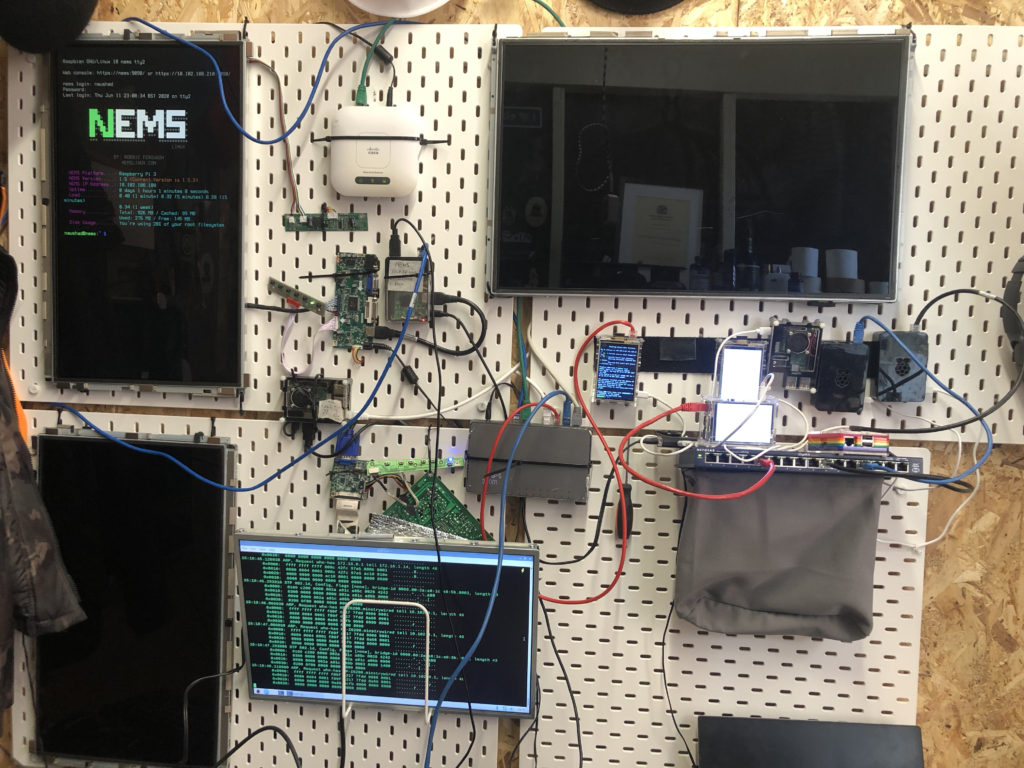
Upgrade: Remote Lab 2020
Penetrating Lab 2010
Penetration testing (also called pen testing) is an attempt to evaluate the security of an IT infrastructure by safely trying to exploit vulnerabilities. These vulnerabilities may exist in operating systems, computer systems, network systems, web application flaws, improper configurations,improper patch management or risky end-user behavior. Such assessments are also useful in validating the efficacy of defensive mechanisms, as well as, end-user adherence to security policies.
Penetration tests are typically performed using manual or automated technologies to systematically compromise servers, endpoints, web applications, wireless networks, network devices, mobile devices and other potential points of exposure. Once vulnerabilities have been successfully exploited on a particular system, testers may attempt to use the compromised system to launch subsequent exploits at other internal resources, specifically by trying to incrementally achieve higher levels of security clearance and deeper access to electronic assets and information via privilege escalation.
Information about any security vulnerabilities successfully exploited through penetration testing is typically aggregated and presented to IT and network systems managers to help those professionals make strategic conclusions and prioritize related remediation efforts. The fundamental purpose of penetration testing is to measure the feasibility of systems or end-user compromise and evaluate any related consequences such incidents may have on the involved resources or operations.
Why Perform Penetration Testing?
Security breaches and service interruptions are costly
Security breaches and any related interruptions in the performance of services or applications, can result in direct financial losses, threaten organizations’ reputations, erode customer loyalties, attract negative press, and trigger significant fines and penalties. A recent study conducted by the Ponemon Institute (2014 Cost of Data Breach Study: Global Analysis) reported the average cost of a data breach for the affected company is now $3.5 million. Costs associated with the Target data breach that occurred in 2013 reached $148 million by the second quarter of 2014.
It is impossible to safeguard all information, all the time
Organizations have traditionally sought to prevent breaches by installing and maintaining layers of defensive security mechanisms, including user access controls, cryptography, IPS, IDS and firewalls. However, the continued adoption of new technologies, including some of these security systems, and the resulting complexity introduced, has made it even harder to find and eliminate all of an organizations’ vulnerabilities and protect against many types of potential security incidents. New vulnerabilities are discovered each day, and attacks constantly evolve in terms of their technical and social sophistication, as well as in their overall automation.
Penetration testing identifies and prioritizes security risks
Penetration testing evaluates an organization’s ability to protect its networks, applications, endpoints and users from external or internal attempts to circumvent its security controls to gain unauthorized or privileged access to protected assets. Test results validate the risk posed by specific security vulnerabilities or flawed processes, enabling IT management and security professionals to prioritize remediation efforts. By embracing more frequent and comprehensive penetration testing, organizations can more effectively anticipate emerging security risks and prevent unauthorized access to critical systems and valuable information.
How Often Should You Perform Penetration Testing?
Penetration testing should be performed on a regular basis to ensure more consistent IT and network security management by revealing how newly discovered threats or emerging vulnerabilities may potentially be assailed by attackers. In addition to regularly scheduled analysis and assessments required by regulatory mandates, tests should also be run whenever:
- New network infrastructure or applications are added
- Significant upgrades or modifications are applied to infrastructure or applications
- New office locations are established
- Security patches are applied
- End user policies are modified
How Can You Benefit from Penetration Testing?
Penetration testing offers many benefits, allowing you to:
Intelligently manage vulnerabilities
Penetration testing provides detailed information on actual, exploitable security threats. By performing a penetration test, you can proactively identify which vulnerabilities are most critical, which are less significant, and which are false positives. This allows your organization to more intelligently prioritize remediation, apply needed security patches and allocate security resources more efficiently to ensure that they are available when and where they are needed most.
Avoid the cost of network downtime
Recovering from a security breach can cost an organization millions of dollars related to IT remediation efforts, customer protection and retention programs, legal activities, discouraged business partners, lowered employee productivity and reduced revenue. Penetration testing helps you to avoid these financial pitfalls by proactively identifying and addressing risks before attacks or security breaches occur.
Meet regulatory requirements and avoid fines
Penetration testing helps organizations address the general auditing/compliance aspects of regulations such as GLBA, HIPAA and Sarbanes-Oxley, and specifically addresses testing requirements documented in the PCI-DSS and federal FISMA/NIST mandates. The detailed reports that penetration tests generate can help organizations avoid significant fines for non-compliance and allow them to illustrate ongoing due diligence into assessors by maintaining required security controls to auditors.
Preserve corporate image and customer loyalty
Even a single incident of compromised customer data can be costly in terms of both negatively affecting sales and tarnishing an organization’s public image. With customer retention costs higher than ever, no one wants to lose the loyal users that they’ve worked hard to earn, and data breaches are likely to turn off new clients. Penetration testing helps you avoid data incidents that put your organization’s reputation and trustworthiness at stake.
Below are the types explaining how a penetration test is performed!
1) Social Engineering:
Human errors are the main causes of security vulnerability. Security standards and policies should be followed by all staff members to avoid social engineering penetration attempt. Example of these standards include not to mention any sensitive information in email or phone communication. Security audits can be conducted to identify and correct process flaws.
2) Application Security Testing:
Using software methods one can verify if the system is exposed to security vulnerabilities.
3) Physical Penetration Test:
Strong physical security methods are applied to protect sensitive data. This is generally useful in military and government facilities. All physical network devices and access points are tested for possibilities of any security breach.
What are the various pen testing techniques:
1) Manual penetration test
2) Using automated penetration test tools
3) Combination of both manual and automated process
The third process is more common to identify all kinds of vulnerabilities.
Manual Penetration Testing:
The thumb that real life hackers follow, is not to use automated tools, but to do the hacking manually. This is because it is not entirely possible for tools and scripts to find all vulnerabilities. There are some vulnerabilities which can be identified by manual scan only. Penetration testers can perform better attacks on application based on their skills and knowledge of system being penetrated. The methods like social engineering can be done by humans only. The same applies to website attacks such as SQL Injection, Cross site scripting (XSS) and cross site request forgery (CSRF). Manual checking also covers design, business logic as well as code verification.
How exactly the pentest is performed?
1) Data collection:
Various methods including Google search are used to get target system data. One can also use web page source code analysis technique to get more info about the system, software and plugin versions. There are many free tools and services available in the market which can give you information like database or table names, DB versions, software versions, hardware used and various third party plugins used in the target system.
2) Vulnerability Assessment:
Based on the data collected in first step one can find the security weakness in the target system. This helps penetration testers to launch attacks using identified entry points in the system.
3) Vulnerability Exploitation:
This step requires special skills and techniques to launch attack on target system. Experienced penetration testers can use their skills to launch attack on the system.
4) Result analysis and report preparation:
After completion of penetration tests detailed reports are prepared for taking corrective actions. All identified vulnerabilities and recommended corrective methods are listed in these reports. You can customize vulnerability report format (HTML, XML, MS Word or PDF) as per your organisation needs.

